Real-Time KERNEL SECURITY (RKP)
What does RKP do?
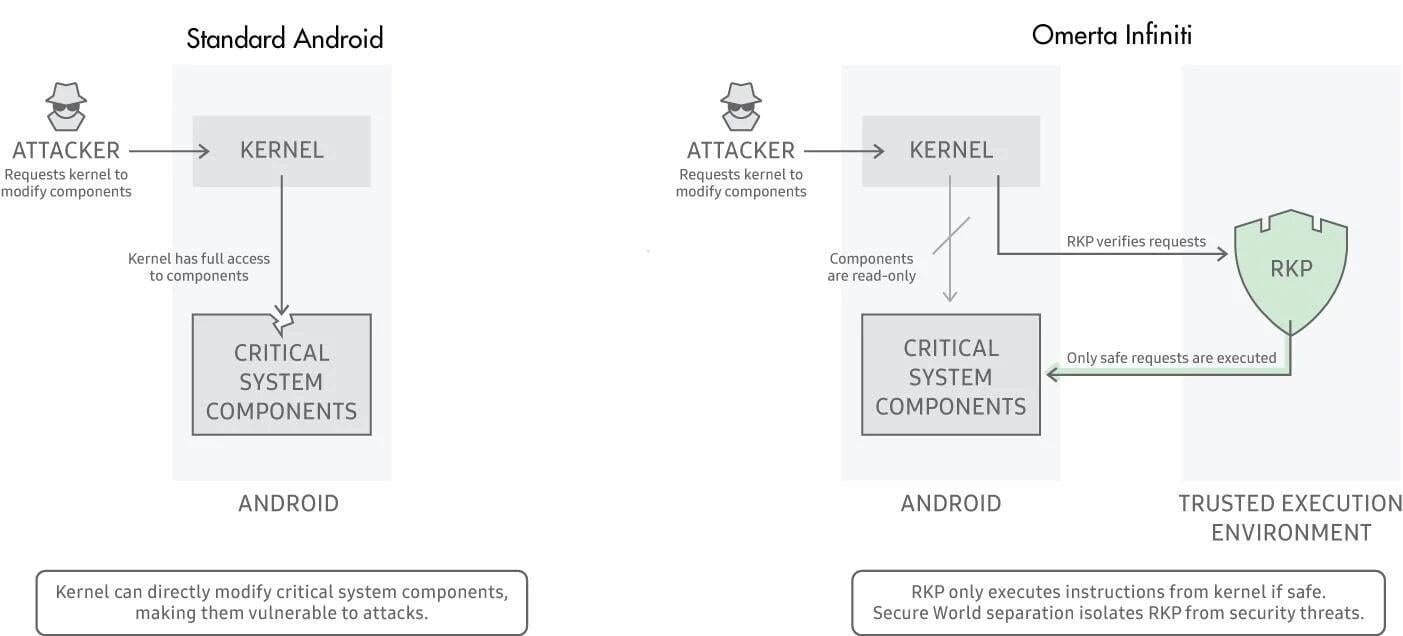
Kernel protection is key to device security & overall operating system integrity. When attackers find software application vulnerabilities, they often escalate privileges as well as compromise the core of the OS: the kernel.
A compromised kernel can leak sensitive data and also even allow remote surveillance as well as control of the affected device. If the kernel itself is controlled at runtime, other more typical securities like Secure Boot or hardware-backed keystores are of little value. After a phone boots and decrypts, a compromised kernel can leak information such as passwords & pins.
RKP Framework
RKP's seclusion from the kernel shrinks available attack surfaces and reduces risk to the kernel. This one-of-a-kind capability allows RKP to detect and also protect against the most unsual kernel attacks. RKP defenses consist of 3 areas:
- Kernel code-- RKP stops adjustment of kernel code and logic.
- Kernel data-- RKP stops alteration of important kernel information structures.
- Kernel control flow-- RKP stops Return-Oriented Programs (ROP) and also Jump-Oriented Shows (JOP) attacks that reuse existing kernel logic to assemble manipulates from the kernel's own code.
HOW IS KERNEL SECURITY FEASIBLE?
A kernel defense system cannot exist completely in the kernel because an opponent could circumvent it if the kernel itself has a flaw. The kernel has the lowest granular control level over the OS and, therefore, typically can't be successfully supervised from any lower level.
RKP works by making use of strategies that regulate device memory management and obstruct and inspect essential kernel actions prior to enabling them to execute. RKP is therefore able to protect against a compromised kernel vaulting defence in depth.
Considering that RKP is always on & needs no management, kernel protection is only possible if it fulfills strict functionality as well as performance requirements. RKP's protections are activated out-of-the-box, meaning the owner need do nothing.
PERIODIC KERNEL MEASUREMENT (PKM)
The TrustZone-based Integrity Dimension Style (TIMA) architecture offers a variety of core features to safeguard against mobile phone breachs. Among these central TIMA features is Periodic Kernel Measurement(PKM).
If legitimate kernel code or information is modified maliciously, pkm will spot and halt the attack. PKM also keeps track of the crucial Security Enhancements(SE) for Android via information structures in OS kernel memory. This stops destructive assaults from damaging and possibly disabling SE for Android.
PKM safeguards the Linux kernel code and web pages from assaults trying todisable SE for Android.
During the phones firmware build, the SHA1 hash of every kernel code, and the read-only information page, is collected into a measurement file. These measurements are signed by Samsung to ensure data integrity and authenticity before inclusion into the firmware.
During device operation, TrustZone-based Integrity Measurement Architecture (TIMA) occasionally recalculates the measurements of the running kernel to compare them to the signed data saved on the device.
When PKM runs, it reads the physical memory addresses made use of by SE for Android to identify:
- SE for Android is enabled
- SE for Android is in enforcement mode.
If destructive code manages to disable SE for Android, or change it to permissive mode, PKM spots the state modification & triggers a defence.
COMPLETE SECURITY PROTECTION
At a 2018 mobile protection meeting, RKP was touted as the best Android defense innovation available and also was credited with the absence of brand-new public exploits in the past year for all Knox devices.
The Real-time Kernel Protection (RKP) is considered the sector's best security against kernel hazards & exploits.
Although RKP is only one layer within Infiniti's defence in depth strategy, it effectively shows the unique protection delivered when hardware, software, and advanced security research are developed holistically. Guaranteeing safety, low maintenance, reliability & industry-leading protection; consumers can count on Omerta Infiniti when in high-security environments.